SPDM Protocol Support
Computers & ServersSecurity Protocol and Data Model over MCTP
What is SPDM?
SPDM (Security Protocol and Data Model) is a DMTF specification for device authentication, measurement, and attestation transported over MCTP. SPDM enables a verifier (typically a BMC or host) to authenticate managed components such as NICs, GPUs, storage controllers, and FPGAs by exchanging certificates, performing challenge-response authentication, and retrieving device measurements. SPDM is becoming a critical requirement in data center security architectures for establishing hardware root of trust. Engineers debugging platform security need SPDM decode to verify the authentication handshake, certificate chain validation, and measurement reporting between the verifier and responder devices.
SPDM Quick Reference
| type | Packet-based |
| signals | MCTP transport |
| features | DMTF device authentication and attestation |
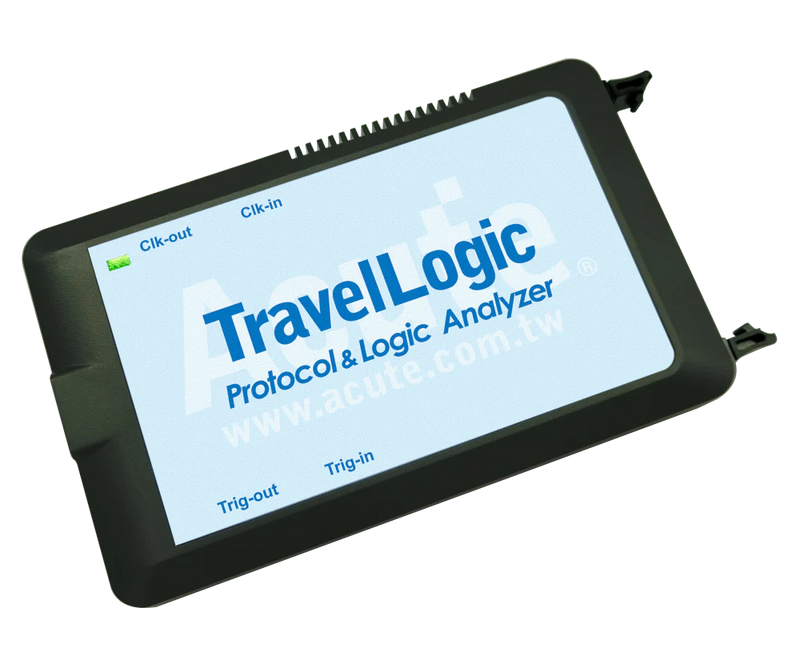
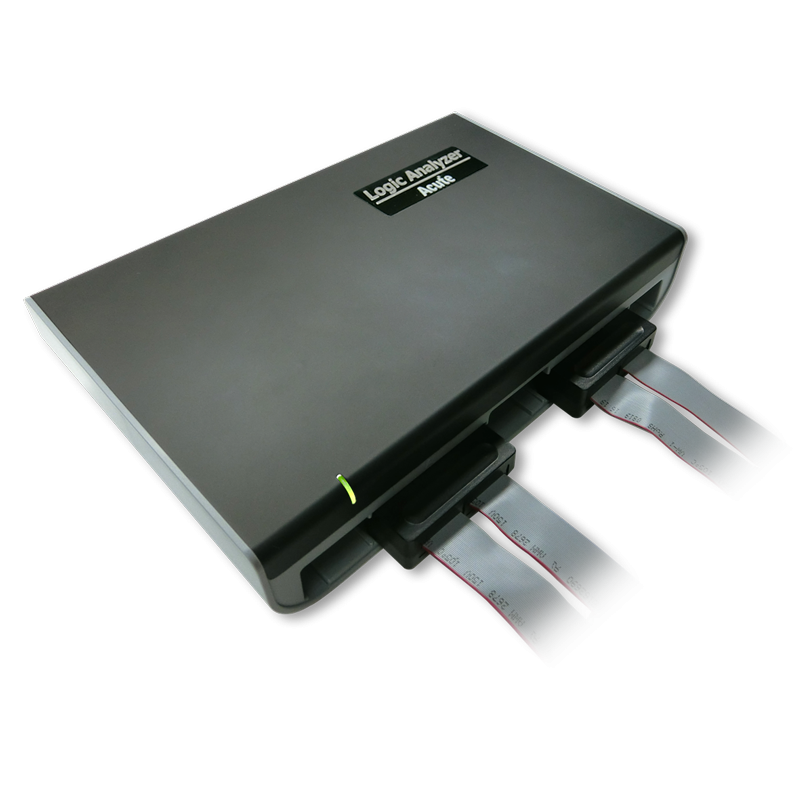
Acute Instruments Supporting SPDM
Ready to analyze this protocol?
See how Acute instruments capture and decode this protocol in real time. Request a demo or contact our team.
How to Analyze SPDM with Acute Instruments
Connect your Acute logic analyzer to the MCTP transport interface carrying SPDM traffic.
Attach a ground lead to the target board's ground reference.
In the Acute software, select the SPDM protocol decoder and assign the transport signals to the correct input channels.
Configure the decoder for the MCTP transport binding.
Capture and view decoded SPDM messages showing GET_VERSION, GET_CAPABILITIES, NEGOTIATE_ALGORITHMS, GET_DIGESTS, GET_CERTIFICATE, CHALLENGE, and GET_MEASUREMENTS exchanges.